Critical IT Change Detection
Detect the critical changes inside the networks you manage that create risk. Whether caused by hackers, internal bad actors, or honest mistakes, Cyber Hawk will sound the alarm on hard-to-detect critical changes in your network.

Improve Managed Security With High-Value Change Detection
More than 70% of cybersecurity incidents today are the result of undetected changes that no firewall could have prevented. Add an essential layer to your IT security and risk management with Cyber Hawk's critical IT change detection and alerting capabilities.
Detect suspicious activities within the networks you manage
Get alerts on potential threats that traditional antivirus software cannot detect. Identify changes that may signal malicious activities. These may include changed access to restricted systems; attempted access to restricted systems by new users; and anomalous end-user behaviors such as logins at unusual hours.
Respond quickly to high priority issues
Quickly triage detected issues with interactive email alerts that rank changes based on severity. Choose to ignore benign or known changes and stop future alerts. For issues that need further investigation, automatically create follow-up tasks in the Cyber Hawk management portal or create PSA service tickets.
Detect changes with artificial intelligence
Proactively safeguard the networks you manage with Cyber Hawk's powerful critical change detection features. With built-in machine learning, it tracks activity over time, establishing patterns and trends that can represent real threats if sudden changes are detected. The longer Cyber Hawk runs on your networks, the smarter it gets.
See How Cyber Hawk Works
In this video, see how Cyber Hawk plays a crucial role in identifying unauthorized or malicious changes in an IT environment that represent potential threats.
Take interactive tourCyber Hawk's Critical IT Change Detection Features
Cyber Hawk finds unplanned, unauthorized and malicious network changes that represent potential threats. It sends you alerts to ensure the integrity, security and stability your network.
Automated scans with minimum setup
Get started detecting changes immediately with minimal configuration. All ongoing adjustments are automated which makes managing your internal threats effortless. The more you use Cyber Hawk, the better it gets.
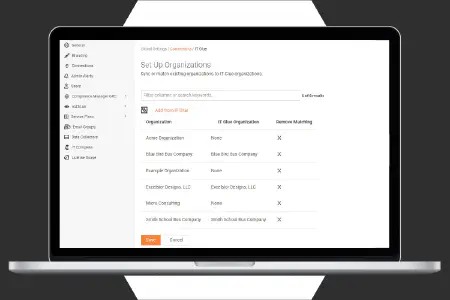
Smart tags customize your experience
Easily customize what Cyber Hawk looks for and ignores based on your specific IT environment. Cyber Hawk's intuitive rules engine, called Smart Tags, is easily managed with a simple check-list menu.
Advanced IT change detection
Cyber Hawk scans the entire network, checking for things that monitoring tools can't see. It analyzes data from end users, assets and configuration settings and finds crucial changes that represent risk.
Direct PSA integration for service tickets
Improve productivity and efficiency with automatic ticket creation in the leading professional service automation (PSA) tools. Cyber Hawk integrates with Autotask, ConnectWise, BMS and TigerPaw One.
React Fast to Critical Network Changes With Cyber Hawk
With cyber threats on the rise, organizations must do everything possible to reduce risk. Critical changes to your network that could signal insider threats. Learn how Cyber Hawk helps discover these changes and protect against them.
Download Now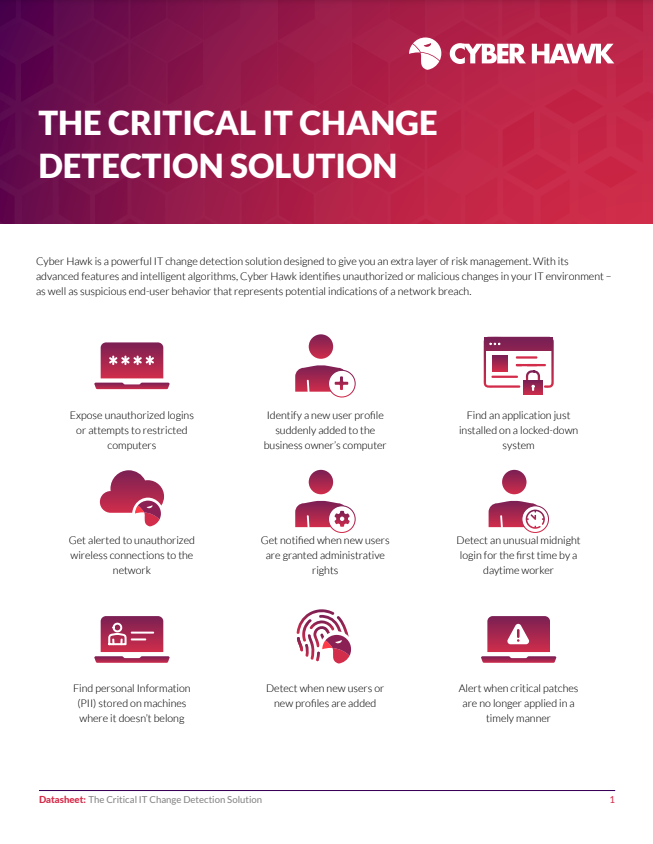
Automated Change Alerts and Summary Reports
Cyber Hawk performs a daily sweep of your entire network and notifies you by email about critical IT change events and activities. It reduces the need for constant manual review of logs and data. Weekly change reports help easily check for less urgent anomalies and changes that warrant further investigation.
Access control changes
Stay informed about important access control changes to prevent potential security breaches. Expose unauthorized logins or new attempts to access restricted computers. Get alerted when a new user profile is added.
Endpoint changes
Be notified about key changes to your endpoints, such as new applications or drives added on locked-down systems, or if critical patches are no longer applied. Quickly identify any unauthorized changes or malicious activities to take immediate action.
Domain user changes
Be notified if users are elevated to domain administrators without your knowledge, whether by accident or through access breach. Reviewe and take action immediately if the change was unauthorized.
Switch port changes
Be alerted to changes in switch port connections that may indicate that someone may be attaching a device to the network, detected by inspecting what is plugged into each switch and comparing to the last connection.
Our Ongoing Innovation in IT Change Detection
We have been able to position Cyber Hawk to our clients across all verticals. As a Managed Security Services provider we work with clients of all types who are bound by various security and compliance frameworks most of which require some facet of monitoring, logging, and reporting. Cyber Hawk is a great solution for them as it meets both their requirements and budget. As an MSP the ease of product acquisition and deployment is a huge plus adding to Cyber Hawk overall value. RapidFire Tools support and product development is probably one of the best among the many vendors we use further helping us extend value added services to our clients.
Affordable and robust critical IT change detection tool.
As a service provider for small businesses we needed a solution that provided actionable intelligence for our clients. Cyber Hawk not only gives us that intelligence, but it does so at a price point that makes it appealing to clients of every size. What we like most about Cyber Hawk is that is allows us to quickly see things we can make even more secure with ease!
Cyber Hawk is hands down a great product, I have implemented in many different industries and continue to impress even the best security admins. With this product I get to play with the big boys.
The Cyber Hawk has been an invaluable product offering for our MSP. Not only does it give us a great foot into the highly lucrative Security field, but it also helps us in increasing revenue by streamlining processes that would usually take a team to process, all in a single unit! We now make this a mandatory part of our MSP complete and comprehensive package. Clients are hesitant at first, but after explaining, and showing them sample reports, they wonder how they can get all this at an affordable price! I cannot say enough good things about this product. It continues to improve, has great support, and actually does what it says it does! Enough said…
We have added many security products, but Cyber Hawk has been the only one that was able to be used by all of our non-security specialized staff to provide relevant information and value right out of the box.
Cyber Hawk has allowed us to have a deeper view of our client networks from accounts getting created, to devices added to the networks, to the wireless networks that they are connecting their laptops. With the wireless network alerts, we can see who is connecting them to Free Wifi (Starbucks, etc.) and can use this information to develop and offer Security Awareness Training to these clients. And with this information we have proof of what they are doing.
Cyber Hawk is hands down a great product, I have implemented in many different industries and continue to impress even the best security admins. With this product I get to play with the big boys.
What we like most about Cyber Hawk is that is allows us to quickly see things we can make even more secure with ease!
Featured Workflow Integrations for Cyber Hawk
As part of the IT Complete Suite, Cyber Hawk works seamlessly with:
Cyber Hawk + IT Network Assessments
Go beyond the changes to see what caused them with the addition of Network Detective Pro.
Explore Network Detective ProCyber Hawk + Vulnerability Management
Detect additional changes to your risk profile with feeds from VulScan directly into Cyber Hawk.
Explore VulScanCyber Hawk + IT Compliance
Use Cyber Hawk to meet specific IT requirements managed through Compliance Manager GRC.
Explore Compliance Manager GRCMSPs
Win new business, expand client relationships, and drive recurring revenue with comprehensive risk management and compliance services. Protect your clients better while earning a greater share of their IT spending.
Explore SolutionsIT Departments
Foster safer, more compliant operations with automated, data-driven IT assessments. Measure risk to optimize and secure your organization.
Explore Solutions