Measure Risk with Automated Network Scanning Tools
Automate collection of data across the entire network to identify and respond to risk. Network Detective Pro is an IT assessment solution that identifies risks and issues, scores their severity and presents them in actionable dashboards and dynamic reports.


Make Your Network Assessments Work for You
Enhance network visibility and gather data from across the IT environments you manage. With Network Detective Pro you can uncover, prioritize, and manage risks and issues.
Improve issue discovery with automated network scanning
Ensure the integrity of your systems with automated data collectors. Network Detective Pro uses non-intrusive data collectors, light-weight discovery agents, and powerful scanners to identify risks quickly.
Respond to incidents and troubleshoot with speed
Reduce risk efficiently with detailed management plans and remediation guidance that scores network threats and issues based on severity. Customize which IT issues are reported and the importance that they are given in an assessment.
Show value with executive and technical reporting
Gain insights with automated reports. From technical reports for documentation and troubleshooting, to high level summaries for executive presentations. Demonstrate your value to any IT stakeholder.
See How Network Detective Pro Works
Staying ahead in the rapidly evolving IT landscape is crucial. Network Detective Pro elevates your network management capabilities by providing an advanced platform for comprehensive network analysis and risk assessments. Network Detective Pro goes beyond traditional IT assessments by offering automated, real-time data collection and analysis across various network environments.
Whether dealing with on-premises, cloud-based, or hybrid systems, this tool ensures you have a complete and current view of your network's health and security posture. Its sophisticated algorithms automatically identify and score risks, enabling you to prioritize your response efficiently. Experience the seamless integration of technical risk assessments, remediation planning, service ticket automation, and executive reporting in one intuitive platform.
Take Interactive Tour Try Network Detective ProPowerful Features for Your Network Scanning and Assessments
Network Detective Pro is a comprehensive solution that provides deep insights into your network infrastructure. Its innovative and powerful capabilities allow you to easily gather information and monitor your network's health, vulnerabilities, and performance.
Full coverage network scanning
Gain increased network visibility through the most comprehensive network scanning techniques. Such as non-intrusive scans on Windows, macOS and Linux, as well as remote data collectors and light-weight discovery agents.
Multiple network assessment types
Reduce risk across multiple threat vectors with a variety of assessments. Focus your assessments on networks, security, cyberattack risk, MS-365 environments or SQL servers. Including Active Directory, Azure AD (Active Directory), AWS (Amazon Web Services) and more.
End-to-end scheduling and automation
Increase the efficiency and frequency of your assessments with automated data collection and analysis. Then Display insights with detailed reporting, while saving time and further minimizing risk.
Standard and proprietary risk scoring
Prioritize risks based on unique risk scoring algorithms as well as industry standard CVSS and Microsoft Secure Scores. Tackle the most important risks first, based on severity, likelihood of threat and impact on your organization.
Online dashboard with drill-down data explorer
Save time by accessing all discovered data from anywhere, any time through the RapidFire Tools online portal. The dashboard displays the summary info you need. Then drill in for the details and guidance on any discovered risk or issue.
Workflow integrations with other applications
Seamlessly convert discovered issues into PSA service tickets, or into ITGlue for updated network documentation. Pull in data from VulScan, Dark Web ID, MS 365 and other apps to generate expanded reports.
Try Network Detective Pro's Cyberattack Risk Assessment feature
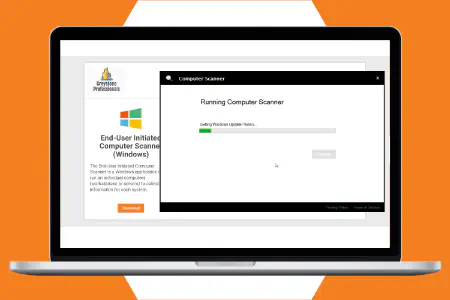
The Cyberattack Risk Assessment is a special feature that makes it extremely quick and easy to remotely spot-check computers on any network and look for hidden vulnerabilities that could be exploited by a successful phishing attack, malicious insider or hacker who has managed to breach your firewall.
Try It For Free
Automated Network Assessment Reports for Every Use Case
Network Detective Pro provides an extensive library of dynamic reports populated with the data from your network scans. The automated branding engine customizes the look and feel of the document to match your organization. Troubleshoot issues faster with technical reports and show key stakeholders the value of what you do.
Our Ongoing Innovation in Network Assessments
Network Detective Pro has helped us find weak points for potential new clients. The information it gathers is incredible! Once new business is won, we use the Network Detective Pro network admin report as the starting point to securing and making our client’s lives easier and more productive. I actually look forward to clients whose report comes back with a 7 or higher because there will be that more sense of accomplishment. Network Detective Pro is extremely easy to use and gathers a tremendous amount of information!
I just closed a deal with a medical practice that has two locations, due in large part to my Network Detective Pro reporting. I really think it gives me the upper hand when I walk in the door - especially if I am bidding against other firms. They can't produce anything near what we show up with on the first day!
The Security Assessment Module of Network Detective has been of great use to our business. We use it in all aspects of our business. We’ve found it to be a great addition when we are doing our initial assessments for clients. Some consultants just give potential clients a “feeling” of how their network stacks up – now we can show them proof! We added it to our suite of provided services for our fully managed service clients, at no extra charge to them. Now they are getting more value for their money! And it gives us yet another point to show clients the value we bring to the table. We also like to use it as an internal check to make sure we are doing our job properly.
We love Network Detective because it saves us time and money while providing a amazing value to our customers. It has replaced hours of work and correlation from our RMM tools with a simple wizard based interface. Our customers love it because it provides excellent benchmarking and documentation
Network Detective has allowed me to enter and document a network initially in 30 minutes. I can show the client the Visio diagram as an initial item, and then print out the entire report binded as their network documentation. The client thinks I spent hours putting it together. In reality, it only took me an hour between collection and printing.
The Security Assessment Module has been fantastic for us. We have been able to go into meetings and really impress the decision makers with the reports generated from the super easy-to-operate interface. We have also made this part of our ongoing services for existing clients, we run the assessments often, generate the report and compare them to previous reports to let clients know we are on top of it. It’s the most impact we have had for a relatively small amount of overhead.
The Network Assessment and Security Assessment modules have allowed Insite to provide better client service, specifically for new customers who are migrating to Insite’s Managed Infrastructure Services. It allows us to quickly get a snapshot of the environment and assess what must be done prior to onboarding the client. It is important that all of our contract customers follow Insite’s best practices to ensure seamless service. The documents produced by the tool are very impressive and help us justify a new proposed service; helping us win new business for both existing customers and new customers.
Featured Workflow Integrations for Network Detective Pro
As part of the IT Complete Suite, Network Detective Pro works seamlessly with:
Network Detective Pro + Vulnerability Management
Network Detective Pro automatically pulls data from VulScan to deliver enhanced risk assessment reports.
Explore VulScanNetwork Detective Pro + IT Change Detection
Cyber Hawk generates alerts for the critical IT changes included in Network Detective Pro's change reports.
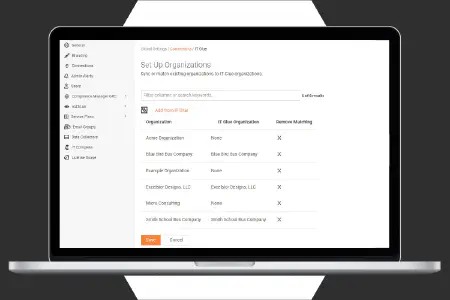
Explore Cyber HawkNetwork Detective Pro + IT Compliance
Network Detective Pro enhances the compliance assessments generated by Compliance Manager GRC.
Explore Compliance Manager GRCMSPs
Win new business, expand client relationships, and drive recurring revenue with comprehensive risk management and compliance services. Protect your clients better while earning a greater share of their IT spending.
Explore SolutionsIT Departments
Foster safer, more compliant operations with automated, data-driven IT assessments. Measure risk to optimize and secure your organization.
Explore SolutionsFrequently Asked Questions About Network Detective Pro and Network Scanning
A network security assessment is a thorough evaluation of how safe an organization's computer network is. It looks at things like the network's structure, systems, and rules to find any possible weaknesses or risks. The assessment involves carefully studying the network's security measures, rules, and ways of doing things to see if they are effective at stopping unauthorized access.
Here is why a network assessment is crucial:
- A network assessment gives you an in-depth analysis of your IT environment to help you make informed decisions regarding system upgrades and overall maintenance.
- It gives you a clear roadmap to help you revamp your IT infrastructure, helping you save money and giving your team the time to focus on strategic activities.
- A strong network assessment gives you full visibility into your organization's network to chalk out a proactive security strategy against global cyberthreats as well as end-user vulnerabilities.
- Network assessments expose loopholes in your current operations, presenting you with opportunities for improvement.
A network assessment should be seen as an invaluable tool for refining critical processes that even the most competent IT pro might have overlooked. However, to get the most out of a network assessment, one must take a holistic approach and include the following crucial components:
Network assets
A network asset is any data, device or component that supports a company's IT infrastructure such as hardware, software and physical devices. The assessment will help identify devices that are obsolete, vulnerable or nearing their end, which in turn will reveal devices that may not be meeting compliance requirements.
IT security framework
There has been a major shift in the cybersecurity landscape, with expert cyberthieves constantly on the prowl looking to exploit system vulnerabilities. This means organizations can no longer merely rely on antivirus and strong passwords. An assessment of the IT security framework helps companies find existing vulnerabilities in their systems and the subsequent security assessment report can help strengthen their infrastructure.
Performance analysis
The aim of an IT infrastructure is to ensure the smooth flow of data. A network assessment helps identify over- or under-utilized technology that affects the overall performance of the network. Based on the analysis, IT pros can allocate resources to enhance system performance.
Cloud setup
With organizations becoming increasingly dependent on the cloud, it is crucial that businesses leverage cloud computing technology. Whether you are using cloud-based services for backup, recovery and file-sharing, or to run cloud-based applications, building a solid security infrastructure is a must.
A network assessment is extremely valuable for IT departments to make more informed and strategic decisions with maximum cost-efficiency. The process can be performed manually by a team of analysts and engineers who will first need to create the assessment and then run tests to get a comprehensive understanding of the IT network. However, this can be tedious and time-consuming.
Through the use of automated network assessment tools, results can be achieved in the timeliest and most resource-efficient way, allowing you to take advantage of advanced capabilities. With an automated tool such as Network Detective Pro, you can scan a massive amount of network, cloud, asset and user data. Its non-intrusive scanners can scan and help you prepare hundreds of customizable reports within minutes without burdening your IT professionals.
A network assessment tool is a software solution that helps businesses streamline and automate network assessments. A network assessment tool has several easy-to-use features that help MSPs and SMBs save time and money, ensuring resources are used effectively. Here are some features to look for in a network assessment tool:
- The ability to non-intrusively collect detailed information on all network assets, including those not physically connected to the network.
- The ability to Identify risks from misconfigurations, network vulnerabilities and user threats.
- The ability to support all environments, from on-premises to remote, to the cloud, to work-from-home
- The ability to produce highly customizable value-proving reports.
Flowbite is an open-source library of interactive components built on top of Tailwind CSS including buttons, dropdowns, modals, navbars, and more.
Whether you are an MSP managing several clients or an SMB, a network assessment tool can help you build an efficient IT management plan. Here is how you can do it:- Admins can use a network work assessment tool to evaluate the overall health of their client's IT infrastructure and identify areas of improvement to further optimize performance.
- You can use a network assessment tool to ensure your business or your clients are in full compliance with necessary regulations by conducting regular network assessments, carrying out remediation efforts to fix the discovered issues and documenting the entire process.
- Companies can utilize network assessment tools to identify network configuration errors that can then be fixed to enhance the security of their network.
- While prospecting for new clients, MSPs can run non-intrusive scans to gauge the scope of work and generate insightful reports to justify the need for their service.
- Both MSPs and businesses can regularly run scheduled automated assessments as part of their IT management plan to maintain network and system health.