Unleash the Power of Vulnerability Management
Discover, prioritize and manage internal and external vulnerabilities. Harden the networks you manage and protect against evolving threats with vulnerability scanning from VulScan.




Harden Your Network With Simplified Vulnerability Management
VulScan is a powerful tool for complete and automated vulnerability scanning. It detects and prioritizes the weaknesses that hackers can exploit, empowering you to harden networks of any size or type and creating an extra layer of cybersecurity protection.
Uncover hidden internal and external vulnerabilities
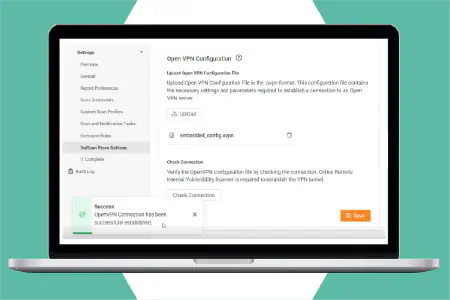
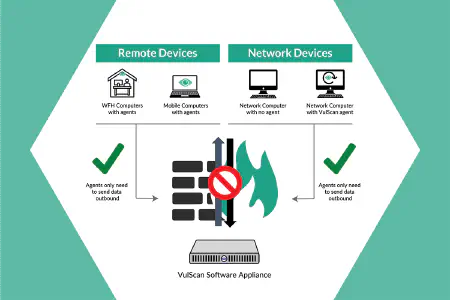
Protect the networks you manage with flexible network scanning options. Vulscan includes on-prem internal network scanners, computer-based discovery agents, remote internal scanning by proxy, and hosted external scanners for comprehensive vulnerability management.
Protect at scale with multi-tenant architecture
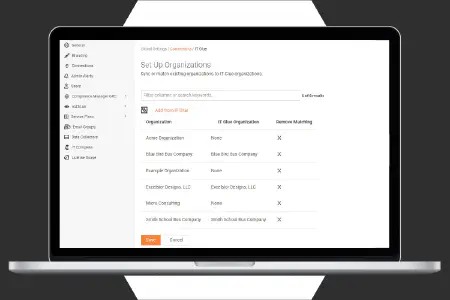
Manage multiple network environments at scale with VulScan's multi-tenant vulnerability management platform. With no limits on the number of scanners you can use on each environment, you can manage multiple networks of any size.
Actionable remediation management plans
Take the guess work out of risk management with accurate risk scoring based on severity. VulScan provides expert issue remediation guidance and known solutions available to further speed up issue fixes.
See How VulScan Works
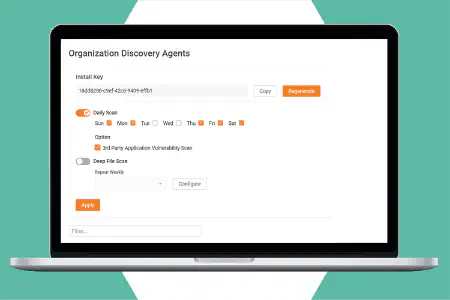
VulScan is the affordable vulnerability scanning solution that works from both inside and outside the networks you manage. It provides the flexibility to schedule scans and filter results for efficient and automated vulnerability management. Access scan results through the user-friendly web management portal. Set up an unlimited number of network scanners using our software and either Hyper-V or VMWare; or install lightweight vulnerability discovery agents on target machines.
VulScan gives you full control over your scanning process to reduce risk and ensure comprehensive protection for your systems.
Take interactive tourVulScan's Vulnerability Management Features
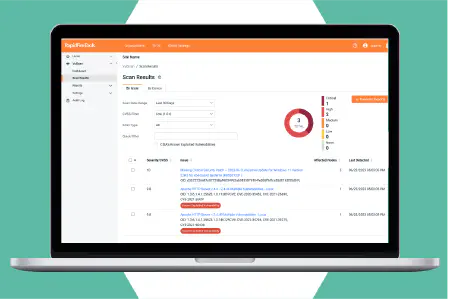
VulScan is an all-in-one solution that uncovers and prioritizes internal and external vulnerabilities in the networks you manage. Quickly flag the most critical vulnerabilities as they appear with its user-friendly dashboards and reports and address them before they can be exploited.
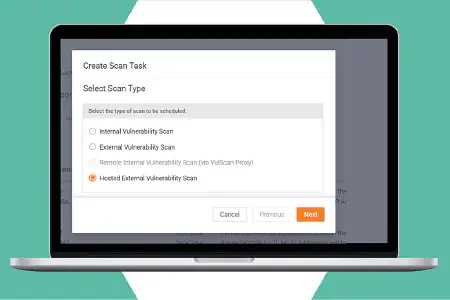
Local and remote internal vulnerability management
Automate full network vulnerability scans to run on any schedule to ensure all network assets are regularly scanned and managed to reduce risk. Options include on-site network scanners, remote internal scanners that you host, as well as individual lightweight discovery agents for Windows machines.
Local and hosted external vulnerability scanning
Set up a scanner on your own remote data center-or any machine outside the target network—to perform external vulnerability scans at multiple locations. Alternatively, access the optional hosted scanner farm for effortless external vulnerability scanning on any site(s) where you perform internal scanning.
Multi-tenant management dashboard
Manage multiple networks through a single online management portal. Dashboard view displays results for all scans, new and remediated vulnerability trends. Filter the results to prioritize your work and get remediation details for easy and effective management of multiple organizations and sites.
Vulnerability noise management
Reduce alert noise from repeating vulnerabilities by marking them as addressed, false positives or addressed to remove them from dashboards, reports and from future notifications. Multiple criteria can be set, including start and end dates, for greater flexibility when suppressing issues and ensuring that only the important and desired vulnerabilities are presented.
Automatic service ticket creation
Save time and ensure remediation can be assigned properly and tracked in PSA systems. VulScan can automatically create tickets for discovered issues and vulnerabilities in Autotask, BMS, ConnectWise and other PSAs. Create tickets for all issues or just those selected during the review process. Further filter results by severity to get the right resources working on the right issues.
Additional power features
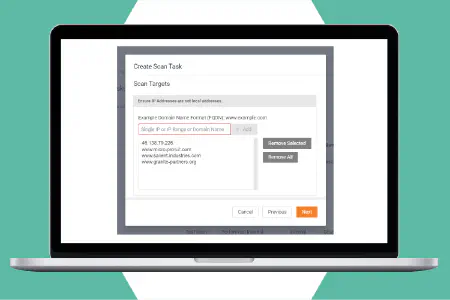
Customize vulnerability scan tasks to target specific IP ranges and TCP and UDP ports during different scans. Run authenticated scans on accounts with credential-secured network endpoints, including computer systems or network devices via SNMP. Attach multiple scanners to the same network to divide the workload and reduce scan time. Scan by IP address, domain name or hostname.
Address Known Network Vulnerabilities With the Right Solution
With over 50 new vulnerabilities discovered every day, no cybersecurity strategy is complete without a plan for vulnerability discovery and management. This guide addresses the most common threats and outlines the tools and processes you need to deal with them.
Download Now
Automated Vulnerability Alerts and Reports
Generate alerts and report output from your vulnerability scans quickly and easily. Use custom filters to focus on the assets you want to include, while screening out issue types, users and CVSS ranges that you want to ignore.
Reports by issue type
Automatically generate reports showing all discovered vulnerabilities organized by type of issue. The report includes all devices that share the same vulnerability, allowing you to apply bulk fixes more efficiently. Includes details about the issue and remediation advice.
Reports by device
Automatically generate reports showing all discovered vulnerabilities on an individual device. For each device listed, the report scores and ranks the issues, giving you the option to address all of them at the same time, or prioritize the work when resources are limited.
Email alerts
Email alerts provide timely notifications regarding completed scans and summary information about the scan results. They help you stay informed about newly discovered critical and high-risk vulnerabilities so you can take quick actions to reduce or eliminate the risk.
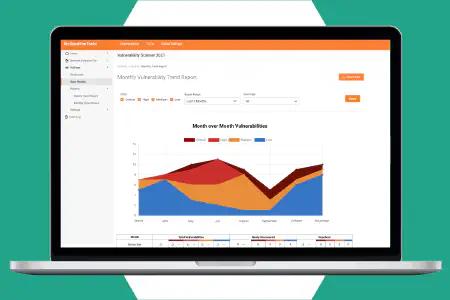
Trending reports
See how your network security posture is changing over time. Trending reports keep a running weekly or monthly tally of newly discovered vulnerabilities-segmented by severity-as well as the number of vulnerabilities that were resolved over the same timeframe.
Our Ongoing Innovation in Vulnerability Management
VulScan has simplified our process for scanning internally and externally, all while giving us the flexibility and scalability our growing organization needs.
It is a very affordable product that is quick to get into production. We are excited to use the product to meet compliance demands and reduce our vulnerability exposure!
VulScan provides the ability to be organized and methodical when adding context for triage and remediation for threats. The integration into Compliance GRC is a HUGE plus!
As a longtime Network Detective user, I am really excited to have a dashboard-view for vulnerabilities that I can share with our customers, and an easy way to create tickets in our ticketing system. Selling vulnerability management and remediation services is a breeze with Vulscan!
VulScan is a reputable product that not only protects your systems. It also protects third party programs. Everything being automated by choice is also an amazing feature. This helps the team collaborate and removes a lot of time that would be needed from other team members. There are many benefits that makes VulScan highly valuable to any IT Department or Company.
VulScan quickly allows you to determine vulnerabilities and see the CVSS scores for each, allowing for easy prioritization of remediation efforts.
We struggled getting into the security aspects of our business, but VulScan has provided an option that didn't require an expert just to get started and has allowed me to dive into the deep end with confidence.
VulScan gives visibility into issue that no other tool in my toolkit can provide. It also gives a great way to track these issues, report false positives and overall manage the vulnerabilities in the system.
Featured Workflow Integrations for VulScan
As part of the IT Complete Suite, VulScan works seamlessly with:
VulScan + IT Network Assessments
Get enhanced vulnerability reports with the workflow integration with Network Detective Pro.
Explore Network Detective ProVulScan + IT Change Detection
Triage issues discovered by VulScan faster, with dynamic alerts generated with the Cyber Hawk workflow integration.
Explore Cyber HawkVulScan + IT Compliance
Run VulScan vulnerability scans directly from inside Compliance Manager GRC
Explore Compliance Manager GRCMSPs
Win new business, expand client relationships, and drive recurring revenue with comprehensive risk management and compliance services. Protect your clients better while earning a greater share of their IT spending.
Explore SolutionsIT Departments
Foster safer, more compliant operations with automated, data-driven IT assessments. Measure risk to optimize and secure your organization.
Explore SolutionsFrequently Asked Questions About the Vulnerability Management Process
A vulnerability scanner is a tool that helps organizations detect security vulnerabilities in their networks, systems and applications that could potentially be exploited by cybercriminals. Based on different configurations and scripts, vulnerability scanning tools run tests on assets that could be exploited. Overall, they bring to light information about the vulnerabilities in an IT environment, degrees of risk from each vulnerability and ways to mitigate a vulnerability.
Vulnerability scanner software only scans what it is configured for. Depending on the type of scan, the tool scans specific interfaces to invoke a response from the targeted devices. For example, if you want the tool to detect outdated operating system versions in your network, it will test the network devices accordingly.
Once it detects a device running on an outdated operating system, it will flag it as a vulnerability in the final scan report. Besides just identifying a vulnerability, certain vulnerability scanning software also review a vulnerability against a database of vulnerabilities to classify it and assign a risk rating to it. In the end, the tool generates a report with all these details.
Vulnerability scanning tools can be divided into five major categories based on the type of assets they scan:
- Network-based scanners: These scanners are focused on identifying security vulnerabilities across a network, for example, unauthorized remote access servers. They assess practices and policies related to both public and private networks.
- Host-based scanners: Such scanners identify vulnerabilities in workstations, servers and other network hosts. In the process, ports and services are scanned vigorously to provide greater visibility into the configuration settings and patch history of assets.
- Wireless scanners: As the name suggests, these scanners specifically assess an organization's wireless network. They successfully identify rogue access points making them crucial in today's hybrid work environment.
- Database scanners: These scanners identify security loopholes, such as misconfigurations, unsecure test environments and other weaknesses, in databases and big data systems.
- Application scanners: This type of scanners play a crucial role in spotting vulnerabilities and misconfigurations in web applications used by an organization.
External vulnerability scans are run from outside an organization's network, targeting areas of the IT environment exposed to the internet such as firewalls, web applications, ports and networks. They unearth vulnerabilities in perimeter defenses like open ports in a network's firewall.
On the other hand, internal vulnerability scans are run from the inside of an organization's network. They detect issues such as vulnerabilities that could be exploited by a hacker who has already made it through perimeter defenses, and threats posed by malware inside a network and insider threats.
Vulnerability scanning helps organizations detect security vulnerabilities such as:
- Outdated and unpatched software
- Missing and poor data encryption
- Operating system and security misconfigurations
- Missing and broken authentication
- Poor cyber awareness and human error
Not only is vulnerability scanning a must-do in today's threat landscape, it is also mandated by nearly every major data protection regulation worldwide. Therefore, vulnerability scanning can't be ignored if an organization must comply with any such standard. Here are some examples:
- General Data Protection Regulation (GDPR): Under Article 32(1), GDPR clearly mandates “a process for regular testing, assessing and evaluation the effectiveness of technical and organizational measures.” Vulnerability scanning is such a process.
- Healthcare Information Portability and Accountability Act (HIPAA): Vulnerability scanning can help organizations — both business associates and covered entities — fulfil at least six specific requirements listed in the Security Rule and Privacy Rule of HIPAA.
- Payment Card Industry Data Security Standards (PCI DSS): PCI DSS clearly states that any organization dealing with cardholder data must implement a process to identify security vulnerabilities and assign a risk rank to any newly discovered vulnerabilities. Vulnerability scanning can help any organization, even if it isn't in the finance industry, to comply with this requirement of PCI DSS.
Apart from these regulations, IT security frameworks suggest vulnerability scanning as a best practice. For example, NIST's Cybersecurity Framework recommends vulnerability scanning for all IT systems as a part of regular IT environment assessments.
Performing vulnerability scans monthly or quarterly can lead to major blind spots and hence, which is why the Center for Internet Security (CIS) recommends weekly or more frequent scans. However, it also recommends organizations to increase patching frequency along with the scanning frequency.